TL;DR:
- Importers face increasing cyber threats such as ransomware, phishing, and third-party breaches.
- Basic cybersecurity measures like two-factor authentication and staff training are crucial for protection.
- Advanced strategies include zero-trust architecture and AI-driven threat intelligence to secure global trade.
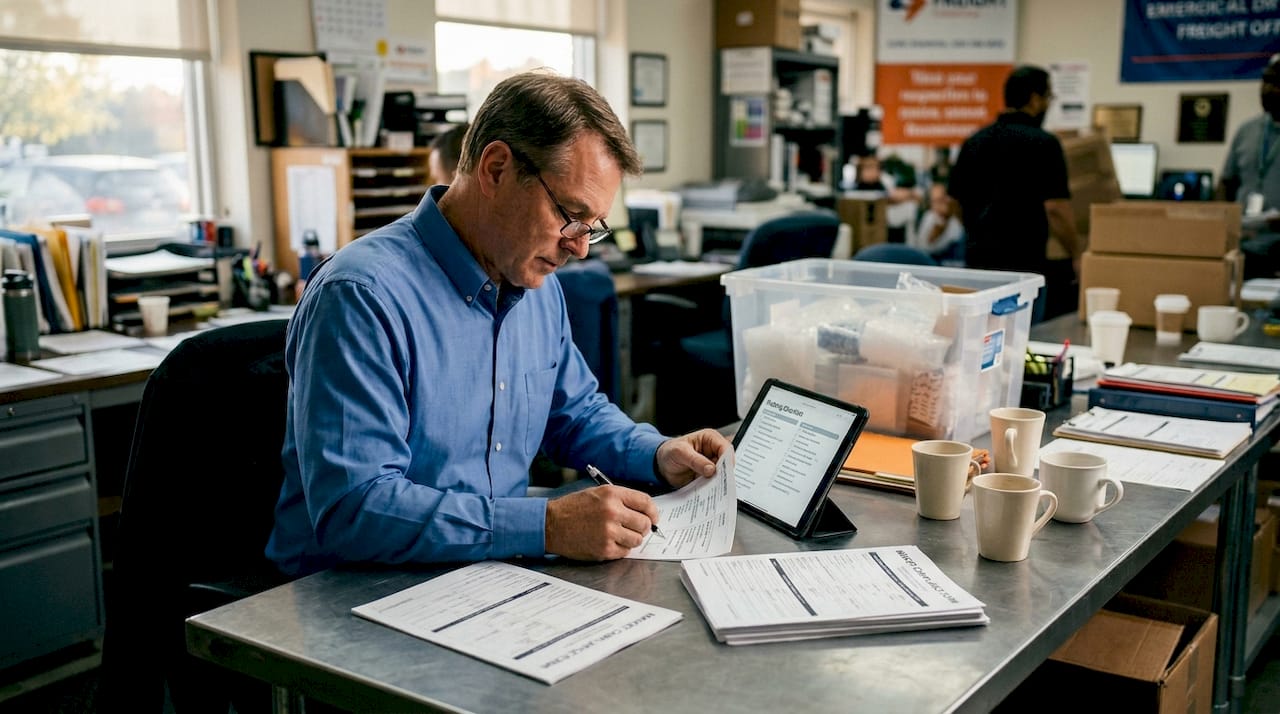
Importers and exporters may be surprised to learn they are now more frequently targeted by cybercriminals than many financial institutions. As global trade digitalizes, heightened cybersecurity risks have followed, with ransomware, phishing, and business email compromise (BEC) threatening sensitive customs and logistics data across interconnected supply chains. The stakes are real: a single breach can freeze shipments, expose confidential trade data, trigger regulatory penalties, and damage supplier relationships built over years. This guide examines why importers face these threats, what practical defenses work, and how compliance programs like CTPAT fit into a stronger security posture.
Table of Contents
- Why importers are vulnerable: Cyber threats in global trade
- Practical cybersecurity measures for importers
- Advanced strategies: Zero-trust, real-time intelligence, and AI
- Compliance and regulatory essentials for U.S. importers
- What most importers miss: Cybersecurity as a business asset
- Secure your import operations with expert logistics solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Importers face rising cyber risks | Modern trade operations make importers frequent targets for ransomware and data theft, demanding proactive security. |
| Immediate security actions matter | Enabling two-factor authentication, encrypted data transfer, and staff education quickly reduces vulnerability. |
| Regulatory compliance is essential | Importers must integrate cybersecurity protocols with CBP, CTPAT, and DOJ mandates to avoid costly penalties. |
| Advanced solutions build resilience | Zero-trust architecture and AI profiling help importers protect data and maintain frictionless trade flows. |
| Supplier vetting reduces third-party risks | Careful onboarding and cybersecurity checks for suppliers are vital to preventing breaches and disruptions. |
Why importers are vulnerable: Cyber threats in global trade
Modern trade operations run on data. Customs declarations, supplier invoices, bill of lading documents, and payment instructions all flow through digital platforms, email chains, and third-party portals. Each connection point is a potential entry for attackers. As supply chain risk impacts become better understood, it is clear that the digital expansion of trade has created new vulnerabilities that many importers have not yet fully addressed.
The most damaging attack types importers face include:
- Ransomware: Malicious software that locks critical systems until a ransom is paid. Expeditors International, a major freight forwarder, suffered a ransomware attack in 2022 that halted global operations for weeks.
- Phishing: Fraudulent emails designed to steal login credentials or trick staff into revealing sensitive data.
- Business email compromise (BEC): Attackers impersonate executives or suppliers to redirect payments or steal shipment data.
- Third-party breaches: A supplier or logistics partner with weak security becomes a backdoor into your own systems.
Per Mondaq’s analysis of logistics cyber threats, ransomware has halted customs and shipping operations at multiple major logistics firms, and IoT and operational technology (OT) vulnerabilities in ports and warehouses are an expanding frontier of risk.
“Rushed supplier onboarding due to tariff disruptions can bypass security vetting entirely, opening doors to unvetted third parties with weak cyber controls.”
Trade policy shifts, such as sudden tariff changes, push importers to source from new suppliers quickly. That urgency often means security checks get skipped. Effective supply chain risk management requires treating cybersecurity vetting as a non-negotiable step in supplier onboarding, not an afterthought.
The financial and operational fallout from these attacks is severe. Beyond ransom payments, importers face delayed shipments, compliance violations from missing or corrupted customs filings, and reputational harm with trade partners. The threat landscape is not slowing down.
Practical cybersecurity measures for importers
To minimize these cyber threats, importers must adopt practical and scalable security measures. The good news is that many of the most effective defenses are not expensive or technically complex. They require consistency and staff buy-in more than large budgets.
Here are the foundational steps every importer should implement:
- Enable two-factor authentication (2FA) on all trade platforms, customs portals, and email accounts. This single step blocks the vast majority of credential-based attacks.
- Use a password manager to generate and store unique, strong passwords for every system. Reusing passwords across platforms is one of the most common causes of breaches.
- Switch to encrypted file transfer for customs documents. Sending sensitive data via email attachments exposes it to interception.
- Maintain regular data backups stored offline or in a separate cloud environment. Backups are the fastest recovery path after a ransomware attack.
- Train staff on phishing recognition at least twice per year. Human error remains the leading cause of successful cyberattacks.
- Establish payment verification protocols. Any request to change banking details or redirect a wire transfer should require a phone confirmation to a known contact.
Per SupplyCheck’s guide on trade cybersecurity, these measures, combined with staff training and verification protocols, form a strong baseline defense for importers of any size.
Pro Tip: Never send customs documents, commercial invoices, or payment instructions as email attachments. Use encrypted sharing links through a verified platform instead. Attachments can be intercepted, forwarded accidentally, or used in phishing schemes.
The table below compares basic versus advanced security tools for importers:
| Security layer | Basic option | Advanced option |
|---|---|---|
| Authentication | 2FA via SMS | Hardware security keys |
| File transfer | Encrypted links | Secure FTP with audit logs |
| Staff training | Annual phishing test | Quarterly simulated attacks |
| Threat monitoring | Antivirus software | AI-driven endpoint detection |
| Incident response | Manual backup restore | Automated recovery playbooks |
Reviewing security filing tips alongside these tools helps importers connect cybersecurity practices directly to customs filing accuracy and compliance.
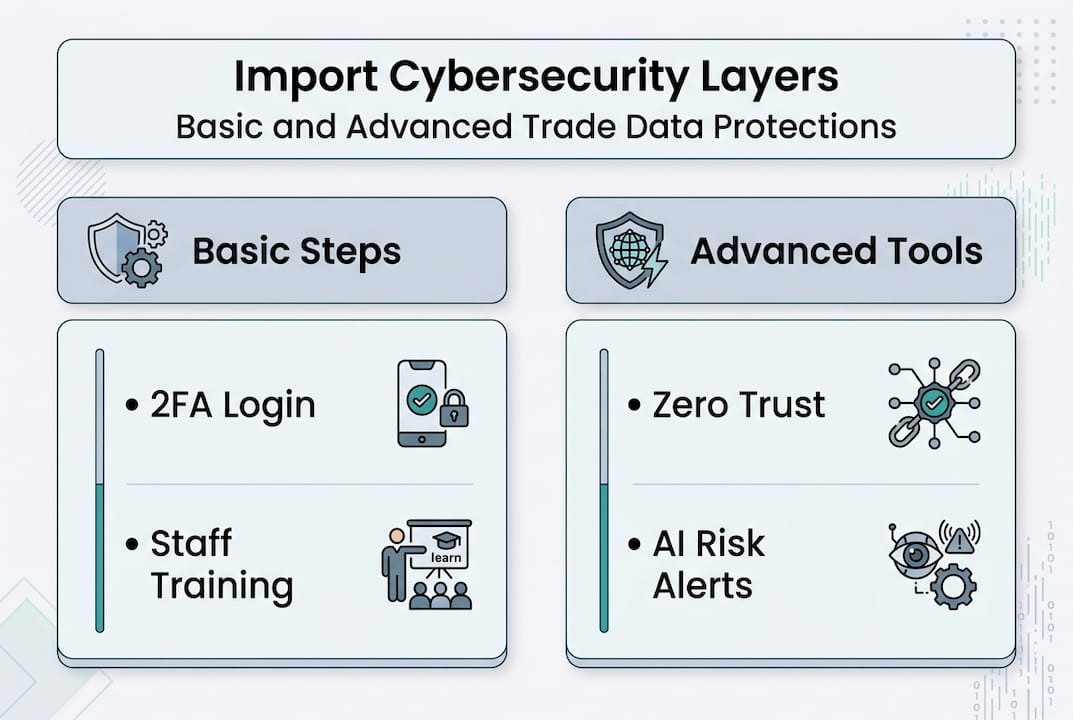
Advanced strategies: Zero-trust, real-time intelligence, and AI
Beyond basics, importers looking for resilience should consider advanced digital security frameworks. Zero-trust architecture is one of the most recommended approaches by cybersecurity experts for trade environments. The core principle is simple: no user, device, or system is trusted by default, even inside your own network.
Key advanced strategies include:
- Least privilege access: Staff and systems only access the data they need for their specific role. A warehouse manager does not need access to payment systems.
- Network micro-segmentation: Dividing your network into isolated zones so that a breach in one area cannot spread across the entire operation.
- Automated incident response: Pre-built playbooks that trigger containment actions the moment a threat is detected, reducing response time from hours to minutes.
- AI-driven threat intelligence: Machine learning tools that analyze patterns across your network and flag anomalies before they escalate.
Per World Economic Forum guidance on supply chain cyber risks, zero-trust architecture, least privilege access, and AI-driven threat intelligence are among the most effective advanced methodologies for protecting trade operations.
Artificial intelligence is also reshaping customs risk management. AI-driven customs profiling uses machine learning to assess importer and supplier risk scores, flagging suspicious patterns without slowing legitimate trade flow. This creates a fascinating dual benefit: faster clearance for compliant importers and stronger detection of anomalies that may indicate fraud or security threats.
Pro Tip: When evaluating AI for shipping security, look for tools that integrate with your existing customs management platform rather than requiring a full system replacement. Incremental adoption is far more sustainable.
Supplier vetting in the context of trade policy disruptions deserves special attention. Tariff changes in 2025 and 2026 have forced many importers to onboard new suppliers rapidly. Each new supplier connection is a potential cyber risk. Reviewing digital freight trends alongside your supplier vetting process helps identify where digital vulnerabilities may be entering your supply chain.
| Framework | Primary benefit | Best for |
|---|---|---|
| Zero-trust architecture | Limits breach spread | Large import operations |
| AI threat detection | Proactive anomaly alerts | High-volume trade data |
| Micro-segmentation | Isolates sensitive systems | Multi-department importers |
| Automated response | Faster incident recovery | Time-sensitive shipments |
Compliance and regulatory essentials for U.S. importers
Importers must not only secure their data but also align with ever-evolving compliance mandates. U.S. Customs and Border Protection (CBP) has made data security a central pillar of its trade programs, and non-compliance carries real consequences.
Key compliance requirements for U.S. importers include:
- CTPAT (Customs Trade Partnership Against Terrorism): Membership requires documented internal controls, self-assessments, and supply chain security protocols. Cybersecurity is now explicitly part of CTPAT criteria.
- Trade Compliance Program: Per CBP’s Trade Compliance Handbook, importers are expected to maintain strong internal controls and regular self-assessments to protect trade data integrity.
- ACAS (Air Cargo Advance Screening): CBP has expanded ACAS data requirements to include IP addresses, MAC addresses, and email identifiers for air cargo security, per Mondaq’s regulatory analysis.
- DOJ Data Security Program: This program restricts data transactions with countries of concern to protect sensitive personal and government data. Importers sharing logistics or customs data with entities in flagged countries face new scrutiny.
Statistic to note: CTPAT members benefit from fewer CBP examinations and expedited processing, making cybersecurity investment directly tied to operational efficiency, not just risk reduction.
Integrating these requirements into daily operations means building compliance checks into your existing workflows. For example, reviewing importer compliance requirements alongside your cybersecurity audit schedule ensures both areas stay current. Similarly, staying informed on international shipping compliance helps importers catch regulatory changes before they create gaps.

The regulatory environment will continue tightening. Importers who treat compliance as a living process rather than a one-time checklist will be far better positioned to adapt.
What most importers miss: Cybersecurity as a business asset
Most importers frame cybersecurity spending as a cost to minimize. That framing misses the bigger picture entirely. Strong cybersecurity is a business asset that offsets risk, strengthens supplier relationships, and unlocks competitive advantages through programs like CTPAT.
Supplier vetting amid trade policy shifts is one of the most underappreciated cybersecurity risks in global trade. When tariffs force rapid sourcing changes, the pressure to move fast often overrides the discipline to vet new partners thoroughly. That gap is where breaches enter.
Per SupplyCheck’s trade cybersecurity framework, cybersecurity for importers is a trade compliance imperative, not a separate IT concern. Integrating security with CTPAT participation and customs data management creates a unified defense that is far stronger than siloed efforts.
Importers who review importer security tips alongside their compliance programs often discover overlapping requirements that can be addressed simultaneously, saving time and reducing redundancy. Cybersecurity, done right, makes the entire import operation more efficient and more trustworthy to trade partners.
Secure your import operations with expert logistics solutions
Protecting sensitive trade and customs data requires more than technology. It requires experienced partners who understand the intersection of logistics, compliance, and security.
Worldwide Express offers customs brokerage services and freight forwarding solutions designed to help importers navigate compliance requirements, streamline documentation, and reduce operational risk. From CTPAT-aligned processes to secure data handling, the team brings deep expertise to every shipment. Explore supply chain risk solutions to understand how a proactive logistics partner can strengthen your security posture. For a broader view of how modern freight forwarding works, the freight forwarding guide is an excellent starting point.
Frequently asked questions
What are the most common cyber threats importers face in global trade?
Importers most often face ransomware, phishing, BEC, and breaches via third-party suppliers, all of which have grown more frequent as trade operations digitalize. These attacks target customs data, payment instructions, and logistics systems that are central to daily operations.
Which cybersecurity steps should importers take first?
The most effective immediate steps include enabling two-factor authentication, training staff against phishing, and using encrypted file transfers for customs documents. These three actions address the most common attack vectors at relatively low cost.
How do U.S. compliance requirements impact cybersecurity for importers?
CBP, CTPAT, ACAS, and the DOJ Data Security Program require strong internal controls and careful data management, including limiting data sharing with countries of concern. Non-compliance can result in increased CBP examinations and loss of trusted trader benefits.
How can importers secure their supply chains against third-party risks?
Importers should prioritize supplier vetting, require cybersecurity awareness from partners, and use zero-trust controls for sensitive logistics systems. Tariff-driven supplier changes in 2025 and 2026 have made this discipline more urgent than ever.
Recommended
- 7 Essential Importer Security Filing Tips for Success – Worldwide Express, Inc.
- Customs clearance for businesses: compliance and smooth trade – Worldwide Express, Inc.
- Master customs compliance tips for smoother shipping – Worldwide Express, Inc.
- Understanding International Trade Compliance Basics – Worldwide Express, Inc.